Hacked? Here's How To Remove The Dreaded Google Malware Warning
As an avid internet connoisseur you've likely seen Google's notorious "Danger: Malware Ahead" warning that curbs traffic, kills profit and effectively shuts down a site for Chrome users. So how does it happen? Well, at any given moment, your website is being scoped and probed by malicious robots on the other side of the planet. These bots, written by hackers, will continuously bombard every server they can find looking for weaknesses. When a weakness is found, your server will be added to a list of targets which will then be subject to a new round of attacks to exploit the weaknesses. And there will be weaknesses.
The general goal of hacking most sites is financial gain. This can come in a variety of ways ranging from relatively harmless spam links and advertisements to extraction of credit card information, remote malware installation, and more. These bots are not usually targeting your site specifically, rather a huge net of sites known to be exploitable, so don't take it personally.
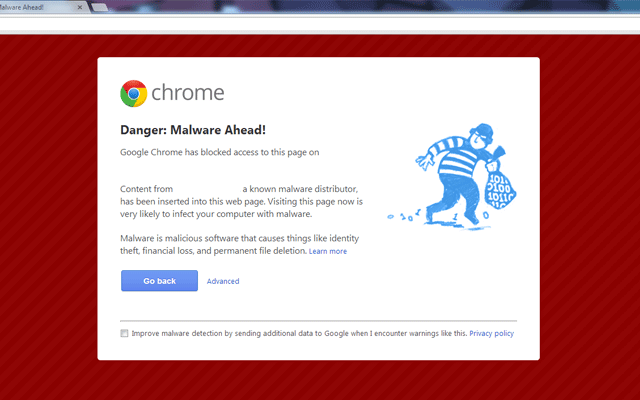
If you find yourself staring at a Google Malware warning screen like this when visiting your site, we're here to help.
What does it all mean?
If your site has been flagged by Google as malicious, it means that a cyber-criminal has successfully exploited your server and installed damaging code in your site. Your site is now blacklisted by Google and every visitor who comes to your site will likely be prevented from reaching the homepage and instead shown an embarrassing malware warning. Even search results where your site appears will be flagged as malicious by Google.

As a website owner/operator, I don't have to tell you how damaging this can be to your traffic and your reputation. The actions you take once you become aware of the problem will determine how long your site will remain flagged, so here is our guide to the steps, strategies, and caveats to disabling these warnings and getting back on Google's good side.
Step 1 - Get Help
The very first thing you should do is contact the technical person in charge of your server that's been hacked.
If that person is you and you don't consider yourself a server administrator, reach out to someone who can help as soon as possible. The same goes if you have a lack of faith in the person handling your server.
The technical skill required to remediate a compromised server is very high. The longer you remain blacklisted by Google, the greater the damage to you or your business, so make sure you've got the right team.
Step 2 - Protect Your Visitors

While the malware warnings should ward off visitors you should prevent your site from doing more harm to your users by quarantining it, or shutting it down entirely. We recommend taking a close look at what occurs from a visitors perspective first. Load up your own website (bypassing all the Google warnings), try to identify the malicious intent, and take note of where it's coming from and what it's trying to do.
By using a tool such as Firebug or Fiddler, you can inspect the communication between your browser and the web to track down the rogue requests. This is helpful because it will not only put you on the trail to sniffing out the problem but also help identify its source, which may not be your main website at all. In a recent case we solved, the issue was a compromised ad server rather than the main site, so we were able to just shut down that portion of the site rather than the entire site while we cleaned the system.
Step 3 - Google Webmaster Tools

Use Google Webmaster Tools to get additional clues on the problem and see what Google saw as the potential threat. If you haven't already done so in the past, you'll need to add your site into Webmaster Tools and verify the ownership of the site by performing one of 4 verification steps. These range from uploading a file via FTP to adding code to your homepage, to modifying the DNS records of your site. Again, the help of a professional is recommended.
Once your site is verified and accessible in Google Webmaster Tools, you can take a look at the "Health" section of your site and review the Malware page to get a list of pages that were flagged and, if you're lucky, a description of the threat and a potential identification of the source.
Regardless of whether or not you think this information will be helpful, you should still set up your domain in Webmaster Tools as you'll need it later to let Google know you've cleaned up the Malware issue.
Step 4 - Search And Destroy

Now that you've got some bearing on where or what the threat is that's prompting the warnings, it's time to hunt it down and clean up the damage. This is, by far, the most difficult part of the process, but the most crucial to disable that nagging Google Malware warning. It's impossible to tell you exactly what to do or where to look because every situation is unique. There are some common skills that you'll require however:
- SSH/Shell administrator access and knowledge
- Database access and SQL knowledge
- An understanding of each component of your site
Again, get help!
Some tips for this step:
- Run a root kit hunter such at rkhunter. It may track down a root kit that would be near impossible to find otherwise.
- Run an antivirus scanner. AVG and Clam both provide free command line scanners.
- Run a shell command to find recently created/modified files such as:
find /path/to/scan -mtime -7
- Disable or remove 3rd party add-ons one by one to try and narrow down the focus
- Follow these tips from Google.
Step 5 - Update And Patch
If you were successful in the previous step and you feel confident that the threat has been removed, you'll want to try and prevent it from happening again.
- Make sure that your server OS and all installed software are up to date.
- Upgrade software (including database engines) as necessary to patch security holes.
- Change the password to all administrative and database accounts.
- Tighten up your firewall.
- Harden your permission levels.
Step 6 - Request A Site Review From Google

In the final step you'll need to request that Google review your site again and hopefully provide a clean bill of health. To do this, log back into Google Webmaster Tools and visit the Health -> Malware page. On that page, click the button to request a site review. Once Google has deemed that you site is no longer compromised the malware warning messages that have haunted you will start to disappear. This may not happen as quickly as you like however.
Since Google is a primary watchdog for this type of problem, dozens of other services will tap into their blacklist to determine what sites are malicious. This includes other browsers like Firefox, but also includes anti-virus companies like Symantec or Malwarebytes. Once they have your site in their own "hacked" lists, users will begin to get warnings about your site that are outside of your control. Even though your site has now been cleared of malware by Google, there is still a period of overlap where visitors may be blocked from your site. In this time it's possible that visitors will continue to report your site as malicious which can cause a viscous cycle of false-positive blacklisting. That is why it's important to act on Step 2 as quickly as possible.
Another caveat to watch out for is subdomains. If your site uses subdomains to house various components of your primary domain, make sure that you load each subdomain into Google Webmaster Tools separately. When it comes time to request the site review, clear all of your subdomains first before requesting a review of the primary domain. The reason for this being, if your primary domain is cleared by Google before a subdomain, and that subdomain is feeding data into your primary domain, then Google will detect that a blacklisted domain is sending data to your clean domain and cause your primary site to be flagged all over again as Malware.
Wrapping Up
Having your system compromised is a nightmare. The extent and duration of that nightmare is completely dependent on the technical resources at your disposal as Google has a fairly straightforward process for removing Malware warnings. The devil is in the details however and the actual removal of the exploit is crucial. It pays to have professionals involved if it's important to your business and uptime is paramount.
Resources
http://www.google.com/webmasters/hacked/
http://googlewebmastercentral.blogspot.com/2013/03/new-first-stop-for-hacked-site-recovery.html
8 Comments
Leave a Reply
Meet the Author

Matthew Mombrea
Matt is our Chief Technology Officer and one of the founders of our agency. He started Cypress North in 2010 with Greg Finn, and now leads our Buffalo office. As the head of our development team, Matt oversees all of our technical strategy and software and systems design efforts.
With more than 19 years of software engineering experience, Matt has the knowledge and expertise to help our clients find solutions that will solve their problems and help them reach their goals. He is dedicated to doing things the right way and finding the right custom solution for each client, all while accounting for long-term maintainability and technical debt.
Matt is a Buffalo native and graduated from St. Bonaventure University, where he studied computer science.
When he’s not at work, Matt enjoys spending time with his kids and his dog. He also likes to golf, snowboard, and roast coffee.


Is it possible that something is setting off that warning, when there really isn't any malware?
Nice article. But how time much does Google take to 'review and reconsider' a site after it has been submitted for reconsideration via Webmasters? It has to be less than 24 hours. Please provide more details regarding this.
Vicky,
Google's review process and timeline are unknown. In our experience the review appears to be largely automated and usually completes in under 24 hours. We've seen cases where it can take as long as 2 - 3 days however.
What do you do when Google incorrectly labels your site as malware? Do they pay the bill when I hire someone to fix it?
Rick,
Doubtful.
I suppose that depends on several factors. Some of which are:
A) Level of inconvenience
B) Damages incurred
C) Number of other users that experience the exact same problem.
D) Willingness of law firm to organize a class action and go after a cash hemorrhaging company like Google.
Time will tell I guess.
Hello Matthew,
Great article, I have a personal blog that got hacked and I did all the steps and it went well. The review was good and website back online in all broswer's but in chrome I still see the warning. Any idea why? I emptied my cache many times to make sure it wasn't the issue... Any thoughts on this situation? Thanks!
Hi Vanessa,
You would need to go to Google Search Console and request a review for your site. If the review is successful, then you won't see the warning again